#239: Learning Lilith
A tentative first step of a difficult task
Welcome to another _secpro!
This week, we learn about how to use Lilith, get acquainted with the landscape in the context of the Iranian crisis, and take a look at the intriguing, possibly slightly terrifying world of quantum cybersecurity - don’t miss out!
Investigative Matters
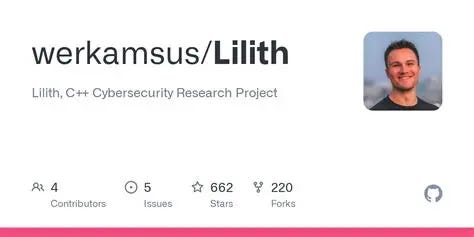
Last week, we asked you - the audience - to give us a heads up on which tool you would like to learn about. After much deliberation, we have found out that our readers want to know a little bit more about Lilith.
Of course, this isn’t a beginner-friendly tool (for that, you might want to look at Metasploit or other more mainstream, accessible tools), however it’s always good to dip your toes into the water with more difficult tools. Take a look at our “beginner’s guide” (but not really for beginners) and see if you can take this valuable and potentially dangerous tool out for a test drive.
News Byte
APT28 Exploiting Routers for DNS Hijacking: Russian state-linked group APT28 is abusing vulnerable routers to perform DNS hijacking, enabling adversary-in-the-middle attacks that steal credentials and authentication tokens at scale.
Iran-Linked Handala Wipes 80,000 Devices via Intune: A single compromised admin credential was used to issue mass remote wipes through Microsoft Intune, demonstrating the destructive potential of identity-centric attacks without malware.
Paste-and-Run Attacks Dominate Initial Access: “ClickFix” social engineering—tricking users into executing clipboard-delivered commands—has become a leading initial access vector, bypassing traditional detection controls.
Mac Infostealers Surge with New Obfuscation Techniques: Atomic Stealer and MacSync Stealer are rising sharply, using AppleScript obfuscation and fake Homebrew prompts to exfiltrate credentials, crypto wallets, and Keychain data.
Vidar Infostealer Returns with Enhanced Evasion: The Vidar malware family has resurfaced with improved anti-analysis techniques and browser injection capabilities following disruption of competing stealers.
SparkCat Malware Expands to Western Targets: A mobile infostealer leveraging OCR to extract crypto seed phrases from screenshots now targets English-speaking users and uses code virtualization for stealth.
Axios Supply Chain Attack via Social Engineering: North Korean actors compromised a maintainer account using fake Teams/Slack interactions, publishing malicious npm packages affecting a widely used HTTP library.
Claude Code Leak Weaponized with Malware: Attackers are distributing trojanized versions of leaked developer tooling, embedding infostealers into widely shared GitHub repositories.
Rise of “Espionage Ecosystems”: Advanced persistent threats are evolving into coordinated ecosystems using AI, fileless malware, and behavioral mimicry for long-term stealth persistence in enterprise networks
Iran-Linked Cyber Operations Persist Despite Ceasefire: Threat actors continue targeting infrastructure and ICS environments, indicating sustained geopolitical cyber activity independent of kinetic conflict pauses.
Taking a look at the academy
Quantum computers could crack cybersecurity systems before 2030 (Jacob Smith):
Explores recent research indicating that advances in quantum computing may render current public-key cryptographic systems obsolete within this decade, forcing urgent migration toward post-quantum cryptography.
AI Helped Spark a Quantum Breakthrough Impacting Encryption: Reports on newly published papers showing AI-assisted breakthroughs accelerating quantum capabilities, with direct implications for breaking modern encryption schemes earlier than expected.
Agentic AI and Cybersecurity Risk Landscape: Examines how frontier AI systems may disproportionately empower attackers over defenders in the near term, reshaping threat models and requiring new defensive paradigms.
Integrating AI-Blockchain Framework with Spider Monkey Optimization for IoMT Security (M. N. Alatawi et al.): Proposes a hybrid AI-blockchain architecture to secure Internet of Medical Things (IoMT) environments, improving resilience against data breaches and unauthorized access.
Cybersecurity Governance under the Jordanian National Cyber Security Framework (JNCSF) (multiple authors, MDPI Journal of Cybersecurity and Privacy): Analyzes governance structures and policy effectiveness in national cybersecurity frameworks, highlighting implementation gaps and optimization strategies.
Future Directions in Cyber Security: Trends, Threats, and Strategic Countermeasures (ResearchGate preprint, March–April 2026 circulation): Identifies emerging threats driven by cloud, AI, and digital transformation, proposing adaptive and layered defense strategies for modern enterprises.
AI-Driven Cybersecurity: Offensive vs Defensive Advantage (Berkeley/industry collaborative research briefing): Argues that AI lowers barriers to entry for cyber attackers more than defenders, emphasizing the need for automated defense orchestration and policy reform.
Cybersecurity Implications of Accelerated AI Adoption in Cloud Systems (PDF): Investigates how AI-driven cloud deployments introduce misconfiguration risks, identity vulnerabilities, and expanded attack surfaces requiring new security models.
Post-Quantum Security Urgency: Cryptographic Transition Challenges: Reviews current academic work on transitioning to quantum-resistant cryptography, highlighting scalability, interoperability, and implementation barriers.